The authenticity of the suspected leak of Intel's Alder Lake BIOS source code has been established, potentially posing a cybersecurity risk to users.
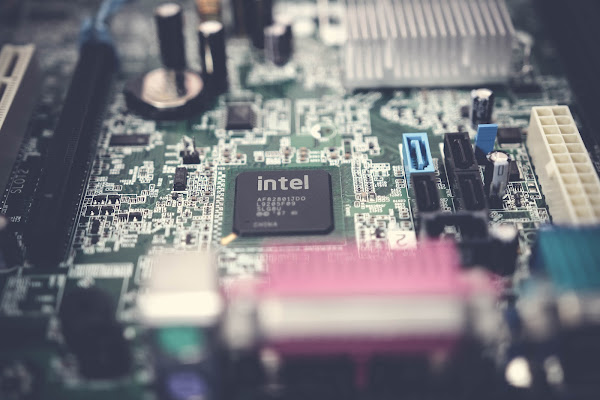
Alder Lake, the firm's 12th generation processor, which debuted in November 2021, is coded for the Unified Extensible Firmware Interface (UEFI) in the released documentation.
The breach, according to an Intel statement provided to Tom's Hardware, does not "reveal any new vulnerabilities since we do not rely on encryption of information as a defense policy."Additionally, it is urging other members of the security research community to use its bug bounty program to submit any potential problems, and it is also alerting customers about the situation.
The 5.97 GB of files, source code, secret keys, patch logs, and compilation tools in the breach have the most recent timestamp of 9/30/22, indicating that a hacker or insider downloaded the data time. Several references to Lenovo may also be found in the leaked source code, including code for 'Lenovo String Service,' 'Lenovo Secure Suite,' and Lenovo Cloud Service integrations.
Tom's Hardware, however, has received confirmation from Intel that such source code is real and is its "exclusive UEFI code."
Sam Linford, vice president of Deep Instinct's EMEA Channels, said: "Source code theft is a very serious possibility for enterprises since it may lead to cyber-attacks. Because source code is a piece of a company's intellectual property, it is extremely valuable to cybercriminals."
This year, there have been multiple instances where an organization's source code was exposed. The password manager LastPass disclosed that some of its source code had been stolen in August 2022, and Rockstar Games' Grand Theft Auto 5 and the Grand Theft Auto 6 version's source code was stolen in September 2022.