Security consultants say hackers can steal information from Google Drive accounts through a method known as password mining. It is all done to conceal the fact that they have taken away a lot of information without leaving any trace behind.
Google Workspace has been found vulnerable to a critical security flaw revealed in the past few days. Thousands of files on people's drives are at risk of silent theft by hackers due to this vulnerability. Due to the current trend of increased remote working and digital collaboration, and as a result of this alarming vulnerability, immediate attention must be given to ensuring the security and privacy of sensitive information.
Mitiga Security researchers discovered a security vulnerability in Google Workspace that was previously unknown. The attacker could use this technique to exfiltrate data from Google Drive without leaving a trace. Due to a forensic vulnerability, this vulnerability allows a user to exfiltrate data from an application. This is without leaving a trail for anyone to see what they did.
There is a security issue pertaining specifically to actions taken by users without a Google Workspace enterprise license. This makes it a particularly serious issue.
There will be no documentation for the actions carried out on private drive-by users without a paid Google Workspace license.
When hackers cancel their paid license and switch to a free "Cloud Identity Free" license, they can disable logging and recording on their computers.
A great collaboration tool that Google offers is Google Workspace. There are, however, several security holes that exist in its security system. There is no such thing as an untouchable threat when it comes to data. When there is a lot of connectivity between things, cloud services can be extremely risky. An entire department's work can be overturned by one wrong link in a chain of documents that are all dependent on one another.
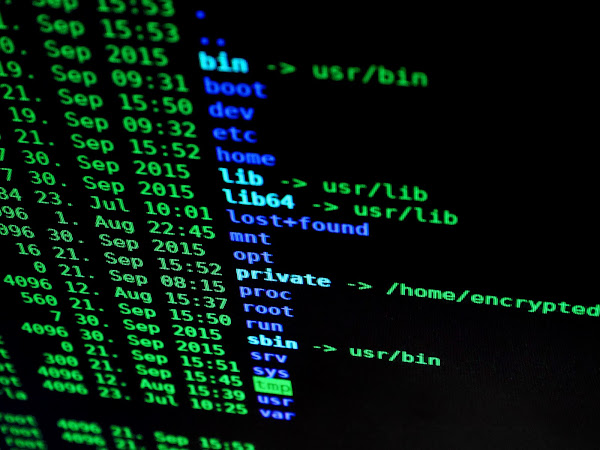
There is a "Cloud Identity Free" license available by default to all Google Drive users. There are no logs kept in the system regarding actions performed by a user on their private drive. This is unless an administrator assigns a paid license to the user. In this environment, due to the lack of visibility, threat actors can manipulate or steal data without being detected. Two different methods can be used to exploit security vulnerabilities in a computer system.
As a first method, a threat actor compromises a user's account, manipulates the license of that user, and allows the threat actor access to and download private files through the user's account. The only thing that is preserved during license revocation and reassignment is the logs that accompany the process. During the revoking of a paid license, the second method targets employees who are involved in the process. Despite being revoked, a license can still be useful for downloading sensitive files from a private drive if the account is not disabled before the license is revoked.
A threat actor could easily revoke a cloud storage account's paid license by following a few simple steps, thereby reverting an account to the free "Cloud Identity Free" license if the account is compromised by a threat actor.
There is no record-keeping or logging functionality in the system, so this would turn it off. Once that was done, they could exfiltrate any files they wanted, without leaving any trace of what they did behind. As far as an administrator is concerned, all they may notice later is the fact that someone has revoked a paid license.
A company called Mitiga says it notified Google that it had found the information, but the company has not responded. An important step of any post-mortem or hacking forensics process is to identify which files have been taken during a data breach so you can conduct your investigation accordingly. It can assist victims in determining what types of information were taken and, as a consequence, if there is a need to worry about identity theft, wire fraud, or something similar, help them establish if they are in danger.
In addition to logging, one of the standard methods by which IT teams keep track of potential intrusions before causing severe damage is to ensure that all activity is logged appropriately. Google Drive accounts, on the other hand, are often left without adequate controls by hackers, which makes it easier for them to steal data undetected.
It is also imperative that cloud storage providers take more robust steps to protect user data to prevent vulnerabilities like this from occurring in the future. Even though Google has yet to reply to Mitiga's findings, the company will likely address this problem shortly.
It will result in an enhanced level of security for its platform as a result.
The users should remain vigilant while they are awaiting the emergence of the attacks and make sure they are protecting their data. It is also recommended that they regularly monitor their Google Drive accounts to make sure that there are no suspicious activities or unauthorized access. Further, it must be noted that strong passwords must be used and two-factor authentication must be used to prevent unauthorized access from happening.
Many documents and files can be stolen, including confidential business documents, proprietary information, financial records, intellectual property, and personal documentation. Regulatory violations, as well as financial fraud, corporate espionage, reputation damage, and other potential economic repercussions, can result from data breaches on a large scale. This is far beyond a mere failure to recover data.
Due to the alarming nature of this discovery, you must take immediate action to protect your sensitive data and protect yourself against potentially harmful hacks.
To improve your organization's security posture, it is recommended you take the following steps:
Make sure two-factor authentication is enabled in your account. Two-factor authentication on your Google Workspace account adds extra security. As a result, even if your login credentials are compromised, this will apply an additional security layer. This will ensure you cannot access your account until you pass an additional verification step.
Stay Educated: Make the most of Google Workspace security alerts and advisories and keep up to date on the latest security threats. It is imperative to keep an eye on official sources, including Google's security bulletins and blogs, for more information regarding security threats.
You need to educate your employees about the risks of phishing attacks. You need to give them the tools to act when interacting with suspicious emails and websites. Educate them about phishing risks and the importance of action when providing login credentials. Reporting suspicious activity promptly should be encouraged as part of organizational culture.













.png)