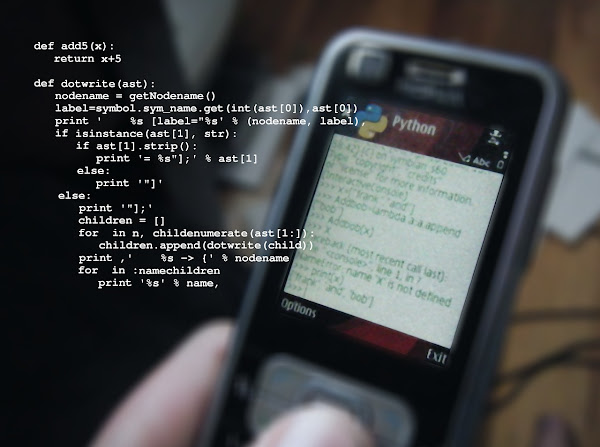
It was discovered today that Vanta, one of the leading providers of compliance automation solutions, experienced a critical product malfunction that resulted in the accidental exposure of confidential customer data. The issue stemmed from a software bug introduced during a recent modification to the company's product code, which inadvertently enabled certain clients to access private information belonging to other customers on the platform.
There has been widespread concern regarding the robustness of the firm's internal safeguards in light of this incident, which reportedly affected hundreds of Vanta's enterprise users. Given its role in assisting businesses with managing and maintaining their own cybersecurity and compliance postures, this incident has raised questions over the firm's internal controls. In response, Vanta's internal teams began investigating the issue on May 26 and implemented containment measures immediately.
The company has confirmed that remediation efforts were fully completed by June 3. Despite this, the incident continues to prompt scrutiny from observers and affected customers regarding the failure of a platform designed to protect sensitive corporate data. The event has also raised concerns about the quality of Vanta's code review protocols, real-time monitoring systems, and overall risk management practices-especially with regard to the scalability of automation technologies in trusted environments.
According to a statement released by Vanta, there was no external attack or intrusion involved, and the incident did not constitute a breach. Rather, the data exposure resulted entirely from an internal product code error that inadvertently compromised data privacy. The company confirmed that the bug led to the unintended sharing of customer data across accounts, particularly within certain third-party integrations. Approximately 20% of the affected integrations were used to streamline compliance with security standards followed by clients.
Vanta, which automates security and compliance workflows for over 10,000 businesses globally, detected the anomaly through its internal monitoring systems on May 26. It launched an immediate investigation and moved quickly toward resolution. The full remediation process was completed by June 3. Jeremy Epling, Vanta's Chief Product Officer, stated that less than 4% of Vanta's customers were affected by the exposure.
All affected clients have been notified and informed of the details of the incident, along with the steps being taken to prevent similar occurrences in the future. Although the exact number of affected organizations has not been disclosed, the scope of the customer base suggests several hundred may have been impacted.
Even though this mid-level data exposure was not widespread, it is a notable incident considering Vanta's role in managing sensitive compliance-related data. It highlights the importance of rigorous safeguards when deploying code changes to live production environments.
To inform impacted clients that employee account data was inadvertently shared across customer environments, Vanta has begun direct outreach. The company explained that certain user data was mistakenly imported into unrelated Vanta instances, leading to accidental data exposure across some organizations.
This internally caused cross-contamination of data raises serious concerns about the reliability of centralized compliance platforms, even in the absence of malicious activity. It underscores that automation platforms, while helpful, can still introduce risk through unexpected internal changes.
For a company positioned as a leader in providing security and compliance services, this incident extends beyond a technical fault-it calls into question the foundation of trust on which such services are built. It also serves as a reminder that automated systems, while efficient, are not immune to the cascading consequences of a single faulty update.
This event highlights the need for organizations to evaluate their reliance on automated compliance systems and to adopt a proactive, layered approach to vendor risk management. While automation enhances efficiency and regulatory alignment, it must be supported by engineering diligence, transparent reporting, and continuous oversight of internal controls.
Businesses should demand greater accountability from service providers-requiring fail-safe mechanisms, rollback strategies, code audit procedures, and more. This incident serves as a key reminder for companies to maintain independent visibility into data flow, integration points, and vendor performance by conducting regular audits and contingency planning.
As the compliance landscape continues to evolve rapidly, trust must be earned not only through innovation and growth but also through demonstrated commitment to customer security, ethical responsibility, and long-term resilience.
Vanta has committed to publishing a full root cause analysis (RCA) by June 16.








.webp)