With the digital age ushering in massive data flows into organizational systems daily, the real value of this data lies in its ability to generate critical insights and predictions, enhancing productivity and ROI. To harness these benefits, data must be efficiently stored and managed in databases that allow easy access, modification, and organization.
Open-source databases present an attractive option due to their flexibility, cost savings, and strong community support. They allow users to modify the source code, enabling custom solutions tailored to specific needs. Moreover, their lack of licensing fees makes them accessible to organizations of all sizes. Popular community versions like MySQL, PostgreSQL, and MongoDB offer zero-cost entry and extensive support.
However, enterprise editions often provide more comprehensive solutions for businesses with critical needs. Enterprise editions are generally preferred over community versions for several reasons in an enterprise setting. A significant advantage of enterprise editions is the professional support they offer. Unlike community versions, which rely on forums and public documentation, enterprise editions provide dedicated, around-the-clock technical support. This immediate support is vital for enterprises that need quick resolutions to minimize downtime and ensure business continuity and compliance.
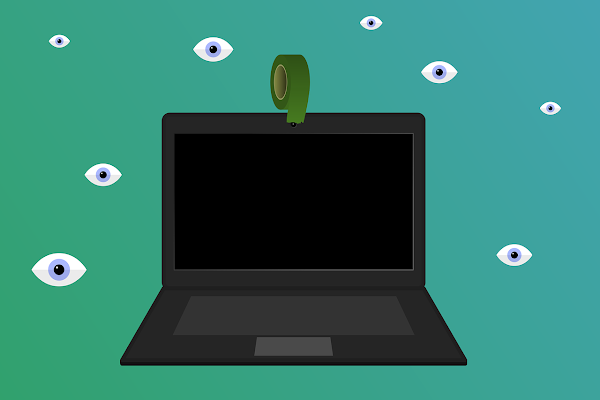
Security is another critical aspect for enterprises. Enterprise editions of open-source databases typically include advanced security features not available in community versions. These features may encompass advanced authentication methods, data encryption, auditing capabilities, and more granular access controls. As cyber threats evolve, these robust security measures are crucial for protecting sensitive data and ensuring compliance with industry standards and regulations.
Performance optimization and scalability are also key advantages of enterprise editions. They often come with tools and features designed to handle large-scale operations efficiently, significantly improving database performance through faster query processing and better resource management.
For businesses experiencing rapid growth or high transaction volumes, seamless scalability is essential.
Features such as automated backups, performance monitoring dashboards, and user-friendly management interfaces ensure smooth database operations and prompt issue resolution.
Long-term stability and support are crucial for enterprises needing reliable database systems. Community versions often have rapid release cycles, leading to stability issues and outdated versions.
In contrast, enterprise editions offer long-term support (LTS) versions, ensuring ongoing updates and stability without frequent major upgrades.
Vendors offering enterprise editions frequently provide tailored solutions to meet specific client needs. This customization can include optimizing databases for particular workloads, integrating with existing systems, and developing new features on request. Such tailored solutions ensure databases align perfectly with business operations.
While community versions of open-source databases are great for small to medium-sized businesses or non-critical applications, enterprise editions provide enhanced features and services essential for larger organizations. With superior support, advanced security, performance optimizations, comprehensive management tools, and tailored solutions, enterprise editions ensure that businesses can rely on their databases to support their operations effectively and securely. For enterprises where data integrity, performance, and security are paramount, opting for enterprise editions is a wise decision.