In 2024, threat actors are likely to evolve tactics to exploit the consolidation of businesses and technologies.
The mid-year 2024 cyber risk report released by Resilience Group indicates that mergers and acquisitions (M&As) are becoming more popular as well as the trend of increased reliance on major software vendors, allowing threat actors to take advantage of new opportunities.
A growing number of threat actors are exploiting business consolidations and technological advancements to launch widespread ransomware attacks, which means organizations need to rethink the way they address new vulnerabilities if they want to remain secure and resilient in the future.
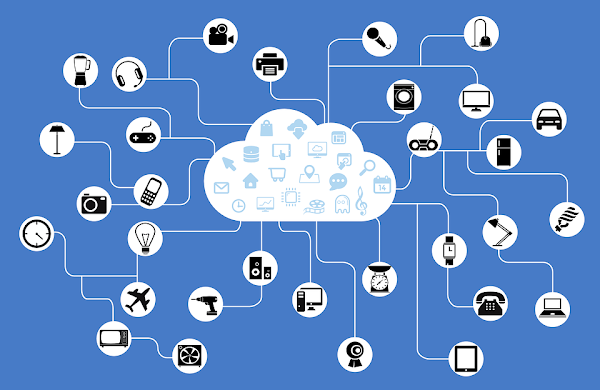
As a result of mergers and acquisitions (M&A) and an increased reliance on key software vendors, cyber security firm Resilience has found that there is a record number of potential points of failure for hackers to exploit, which has resulted in the most damaging cyber incidents of the last year, resulting in an unprecedented number of potential points of failure.
According to the latest statistics, ransomware is the leading cause of financial losses around the world. Using the 'business and technology consolidation' as an opportunity to benefit from the consolidation of business and technology, threat actors have evolved their tactics in 2024 according to Resilience, a leading provider of cyber risk solutions which published its Midyear Cyber Risk Report 2024.
Due to the increased integration of software vendors into the marketplace as well as the reliance on a single point of failure, threat actors have been able to unleash widespread ransomware campaigns by exploiting disparities between the many vendors.
During the past year, we have witnessed some of the most disruptive cyberattacks possibly in the history of mankind, many of which involved heavily interconnected systems or recently acquired companies, which had devastating effects—even causing a range of economic sectors to undergo disruptions.
As part of the Midyear 2024 Cyber Risk Report, released today by Resilience, Resilience has analyzed trends in hacking activity, as well as industry responses to hacking, based on data from our Threat Intelligence team and insurance claims portfolio. As noted in Resilience's report, threat actors have evolved their tactics to take advantage of the increased consolidation of businesses and technology, which has increased ransomware campaigns when compared to the previous year.
There have been increasingly more campaigns targeting interconnected systems and newly acquired companies, posing substantial risks to a variety of economic sectors due to the exposure.
Moreover, the report stated that 35% of all claims made since the beginning of 2023 were due to breaches or ransom attacks caused by third parties. By 2024, there is an expectation that this percentage will rise to 40% and is expected to continue on its upward trajectory.
A recent study by Resilience explained that technology consolidation, in which industries rely on one or a few companies for critical platform services, has proved to have catastrophic consequences downstream when a single vendor is breached, wrote Marykate Broderick for Resilience. Besides the ransomware itself, impacted organizations may also have to pay significant income losses due to business interruptions, as well as ransom payments in addition to the possibility of finding themselves liable for ransoms."
Based on the results of the Claims Data for the year 2024, the manufacturing and construction industries have been reported to have had the highest growth in the number of claims made. The number of manufacturing damage claims surged by 41.7% in 2024, compared to 15.2% in 2023, and the number of construction damage claims also increased by 6.1% within the same time frame.
This quarter, Resilience, revealed that the majority of claims have been filed at the company due to several ransomware attacks, as well as exploits of two zero-day vulnerabilities that were found in the PanOS operating system during the first quarter of 2024. Ransomware, a crypto-currency attack, that took place in February on Change Healthcare, greatly impacted the company's billing and care authorization systems, along with the company's overall operations as a whole. Due to the attack, the US healthcare system has been hit by wide-ranging disruptions affecting hospitals and pharmacies all over the country.
It took UnitedHealth Group, the parent company of Change Healthcare, a considerable amount of time and effort to thoroughly recover and rebuild the affected platforms from scratch to restore service to the patients.
In June 2024, CDK Global, a company that provides cloud-based software for automobile dealerships, suffered from a ransomware attack, which resulted in significant disruptions to the company's operations.
There are approximately 15,000 car dealerships across the US that have been forced to turn their IT systems off, and some have also decided to revert to manual processes to keep the business operating.
As a result of the attack, which is believed to be the work of the BlackSuit ransomware group, severe economic consequences have also been brought on to the company, with estimates of around 100,000 vehicle sales being affected.
Recently, the Federal Bureau of Investigation (FBI), a unit of the United States Department of Justice, confirmed that it had successfully disrupted a criminal ransomware group that was known as "Radar" or "Dispossessor."
An operation by the FBI's Cleveland division was instrumental in dismantling the key infrastructure linked to the group, including servers in the United States, United Kingdom, and Germany, in response to the investigation. In addition to several criminal domains being taken offline as part of the crackdown, the FBI executed the operation in collaboration with international partners. These partners included the UK’s National Crime Agency and law enforcement agencies in Germany. This coordinated effort underscores the increasing severity and sophistication of ransomware attacks, which have escalated as cybercriminals continue to demand larger ransoms each year.
Bayer emphasized the need for business leaders to be prepared for the growing ransomware threat landscape, which he described as increasingly treacherous. He advised that by conceptualizing these attacks as inevitable rather than remote possibilities, organizations can better prepare by investing in cybersecurity personnel, processes, and technology. Such proactive measures will enable businesses to recover more quickly from attacks, minimizing disruption to their operations.
















.jpg)