A Farsi-speaking threat actor believed to be aligned with Iranian state interests is suspected of carrying out a new cyber campaign targeting non-governmental organizations and individuals documenting recent human rights abuses in Iran, according to a report by HarfangLab.
The activity, tracked in January 2026 and codenamed RedKitten, appears to coincide with nationwide unrest that erupted in Iran in late 2025 over soaring inflation, rising food prices, and currency depreciation. The protests were followed by a severe security crackdown, mass casualties, and an internet blackout.
“The malware relies on GitHub and Google Drive for configuration and modular payload retrieval, and uses Telegram for command-and-control,” HarfangLab said.
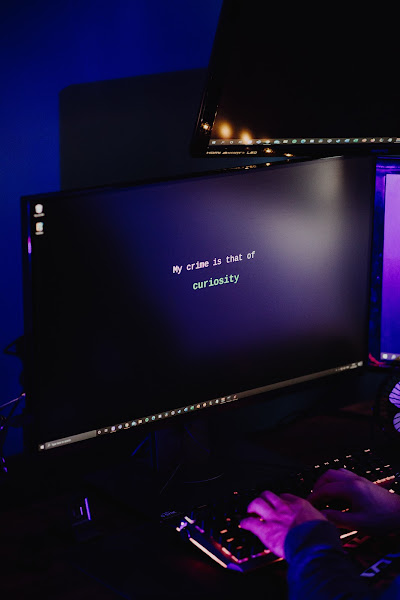
Researchers said the campaign is notable for its apparent use of large language models to help develop and coordinate its tooling. The attack chain begins with a 7-Zip archive bearing a Farsi filename, which contains malicious Microsoft Excel files embedded with macros.
The XLSM spreadsheets purport to list details of protesters who died in Tehran between Dec. 22, 2025, and Jan. 20, 2026. Instead, the files deploy a malicious VBA macro that acts as a dropper for a C# implant known as AppVStreamingUX_Multi_User.dll using a technique called AppDomainManager injection.
HarfangLab said the VBA code itself shows signs of being generated by an LLM, citing its structure, variable naming patterns, and comments such as “PART 5: Report the result and schedule if successful.”
Investigators believe the campaign exploits the emotional distress of people searching for information about missing or deceased protesters. Analysis of the spreadsheet data found inconsistencies such as mismatched ages and birthdates, suggesting the content was fabricated.
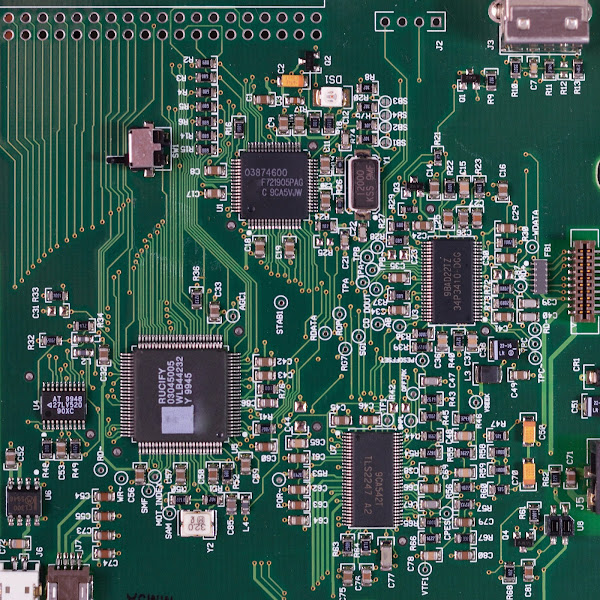
The implanted backdoor, dubbed SloppyMIO, uses GitHub as a dead drop resolver to obtain Google Drive links hosting images that conceal configuration data using steganography. This data includes Telegram bot tokens, chat IDs, and links to additional modules.
The malware supports multiple modules that allow attackers to run commands, collect and exfiltrate files, establish persistence through scheduled tasks, and launch processes on infected systems.
“The malware can fetch and cache multiple modules from remote storage, run arbitrary commands, collect and exfiltrate files and deploy further malware with persistence via scheduled tasks,” HarfangLab said. “SloppyMIO beacons status messages, polls for commands and sends exfiltrated files over to a specified operator leveraging the Telegram Bot API for command-and-control.”
Attribution to Iranian-linked actors is based on the use of Farsi-language artifacts, protest-themed lures, and tactical overlaps with earlier operations, including campaigns associated with Tortoiseshell, which previously used malicious Excel documents and AppDomainManager injection techniques.
The use of GitHub as part of the command infrastructure mirrors earlier Iranian-linked operations. In 2022, Secureworks, now part of Sophos, documented a campaign by a sub-group of Nemesis Kitten that also leveraged GitHub to distribute malware.
HarfangLab noted that reliance on widely used platforms such as GitHub, Google Drive, and Telegram complicates traditional infrastructure-based attribution but can also expose operational metadata that poses risks to the attackers themselves.
The findings follow recent disclosures by U.K.-based Iranian activist and cyber investigator Nariman Gharib, who detailed a separate phishing campaign using a fake WhatsApp Web login page to hijack victims’ accounts.
“The page polls the attacker’s server every second,” Gharib said. “This lets the attacker serve a live QR code from their own WhatsApp Web session directly to the victim.”
That phishing infrastructure was also designed to request access to a victim’s camera, microphone, and location, effectively turning the page into a surveillance tool. The identity and motive of the operators behind that campaign remain unclear.
Separately, TechCrunch reporter Zack Whittaker reported that related activity also targeted Gmail credentials using fake login pages, impacting around 50 victims across the Kurdish community, academia, government, and business sectors.
The disclosures come amid growing scrutiny of Iranian-linked cyber groups following a major data leak affecting Charming Kitten, which exposed details about its operations and a surveillance platform known as Kashef. Gharib has also highlighted leaked records tied to Ravin Academy, a cybersecurity school linked to Iran’s Ministry of Intelligence and Security, which was sanctioned by the United States in 2022.