Passkeys have become a popular method for authentication, offering an alternative to traditional passwords. However, despite their advantages, there are several key issues that need to be addressed. This article explores the problems associated with passkeys and the need for further improvements in authentication methods.
Passkeys, often referred to as passwordless authentication, aim to provide a more convenient and secure way to access accounts and devices. Unlike passwords, which can be forgotten, stolen, or easily guessed, passkeys utilize unique characteristics of the user's device, such as biometrics or hardware-based keys, to grant access.
One of the primary concerns with passkeys is their reliance on specific devices or platforms. For instance, a passkey that works on an Android device might not be compatible with an iOS device or a different operating system. This lack of cross-platform compatibility limits the usability and convenience of passkeys, as users may need multiple passkeys for different devices or services.
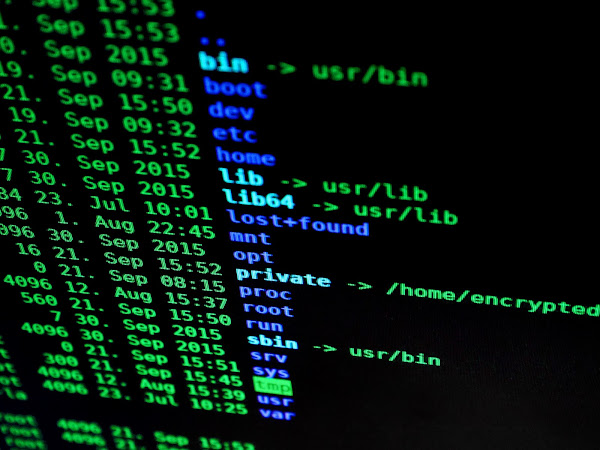
Additionally, passkeys are vulnerable to potential security risks. While they eliminate the need for passwords, which are often weak and prone to hacking, passkeys are not immune to threats. If a passkey is compromised, it could lead to unauthorized access to the associated account or device. Furthermore, if the passkey is stored insecurely, such as in the cloud or on an easily accessible device, it could be accessed by malicious actors.
Another challenge is the adoption and support of passkeys across various platforms and services. Although major tech companies like Google have introduced passkey support, it requires widespread adoption from service providers and developers to offer a seamless experience for users. If passkey support remains limited, users may still need to rely on traditional password-based authentication methods.
To address these issues, further advancements in passkey technology and authentication methods are necessary. First and foremost, there should be greater collaboration between tech companies and service providers to establish standardized protocols for passkey implementation. This would enable interoperability across different platforms, making passkeys more accessible and user-friendly.
Enhancing the security of passkeys is also critical. Additional layers of protection, such as multi-factor authentication, can be integrated with passkeys to add an extra level of security. This could include biometric verification, device attestation, or behavioral analysis to ensure the legitimacy of the user.
Furthermore, educating users about the importance of passkey security and best practices is crucial. Users need to understand the risks associated with passkeys and be encouraged to store them securely, preferably using hardware-based solutions or secure vaults.